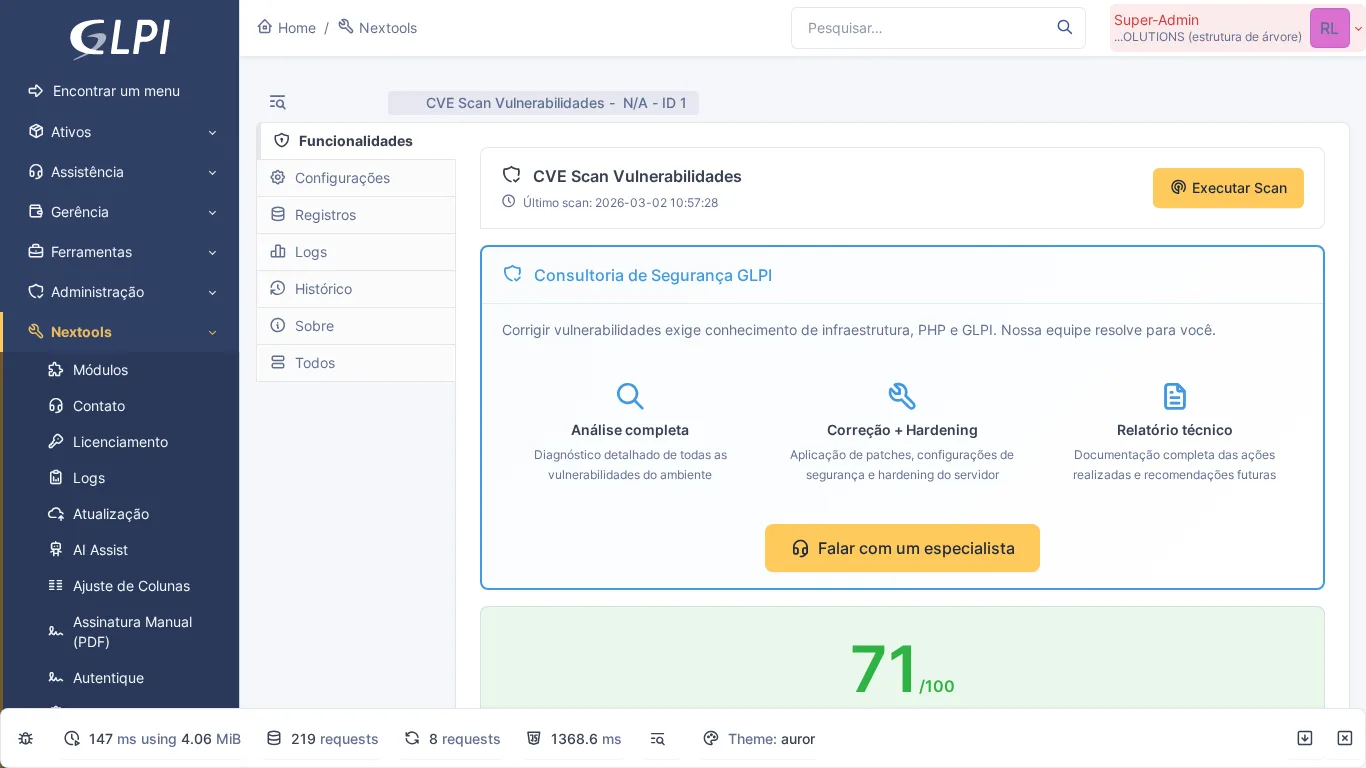
Is your GLPI instance exposed to known vulnerabilities? – The NexTool CVE Scan module answers this question in seconds, cross-referencing the installed version with public CVE databases and auditing 17 critical environment points.
The problem
IT teams operating GLPI rarely have a formal process for tracking CVE vulnerabilities associated with the production version. The NVD (NIST) and GitHub Advisory Database continuously publish CVEs, but manual tracking is impractical in the daily routine of a service desk.
Beyond the software version, the PHP environment and server configurations introduce silent risks: display_errors enabled in production, session cookie without HttpOnly flag, absence of headers like Content-Security-Policy – each detail is a potential attack surface.
Without consolidated visibility, these problems only appear after an incident. CVE Scan was created precisely to anticipate this scenario.
How CVE Scan works
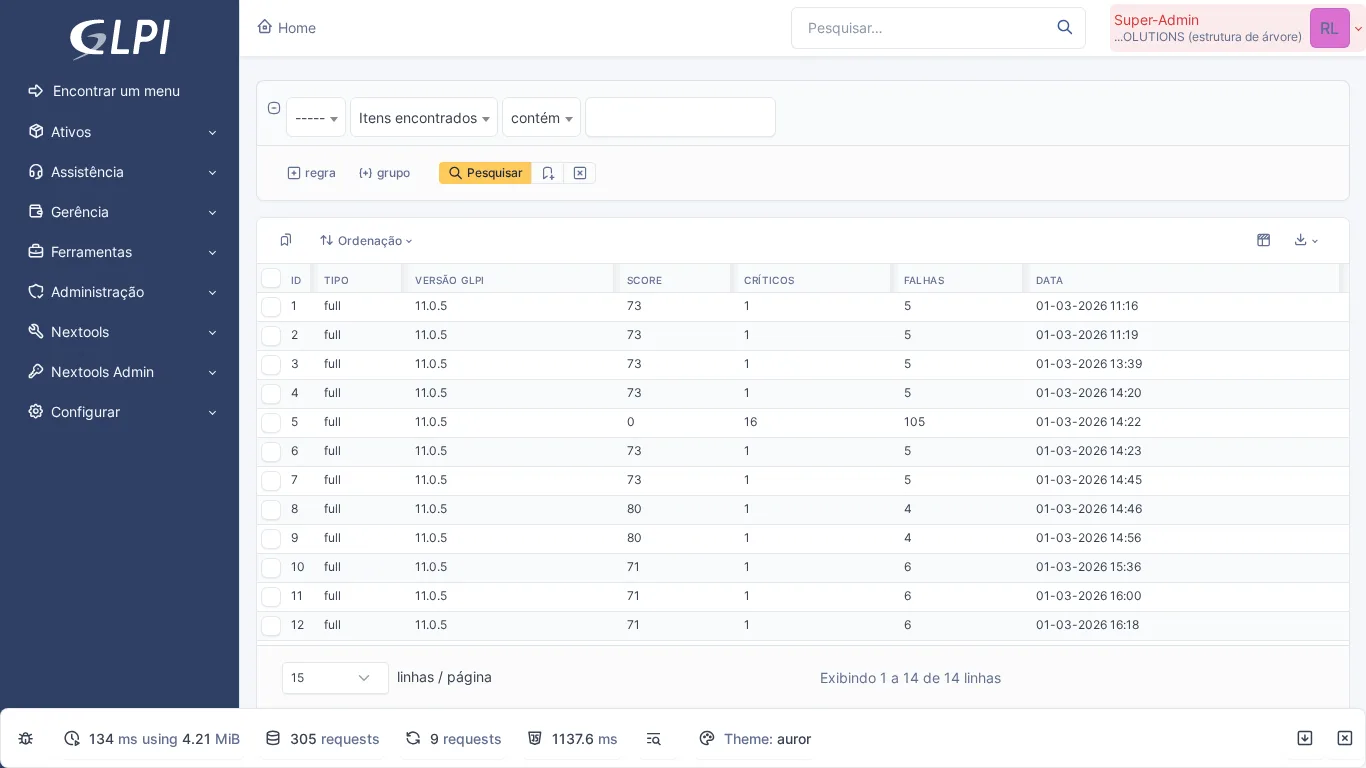
When executing the scan, the module automatically detects the GLPI version via the GLPI_VERSION constant and cross-references it with a dynamic CVE database composed of three sources:
- GitHub Advisory Database – advisory links and details of reported flaws.
- NVD / NIST – authoritative source for CVSS scoring and official metadata.
- 22 static fallback CVEs – ensure coverage even without access to external APIs.
The merge is done by CVE ID: NVD prevails for CVSS, GitHub provides advisory links. A local cache is updated daily via cron and on demand with each manual execution.
Alongside the CVE Scan, the module runs 17 security checks of the environment, grouped into four categories:
- PHP Configuration (8 checks) –
display_errors,expose_php,allow_url_include,session.cookie_httponly,session.cookie_secure, and others. - GLPI Checks (3 checks) – presence of the
install/directory, active debug mode, andconfig_db.phppermissions. - HTTP Headers (3 checks) –
X-Frame-Options,Content-Security-Policy, andStrict-Transport-Security. - Other checks (3 checks) – PHP version at EOL, server software, and additional environment check.
The result is consolidated in a Security Score from 0 to 100 with color coding: red (0–40 – critical), yellow (41–70 – moderate), and green (71–100 – healthy). Each item includes a status indicator (vulnerable or fixed_in_newer), the version that fixes it, and remediation instructions.
How to activate
- Install the NexTool plugin on GLPI.
- Go to Setup > NexTool > Modules.
- Find the CVE Scan card and click Install, then Activate.
- Access the module and click Run Scan in the Features tab.
- Optionally, enter a GitHub token and an NVD API Key in the Settings tab to increase request limits.
Who is it for
The module is ideal for GLPI administrators who need a quick and recurring security audit, IT teams that go through internal or external audits and need evidence of the environment's state, and managers who want to track security posture evolution over time via scan history.
Compatibility
- GLPI: 10.x and 11.x
- Plan: FREE
- Plugin: NexTool 3.x+
Next step
CVE Scan is part of NexTool, a modular plugin for GLPI. Explore all modules or contact the team for a complete security consultation.
This content was produced with the assistance of artificial intelligence and reviewed by the Nextool Solutions team. Screenshots are from the real GLPI environment with the NexTool plugin.